5 Tricky Interview Questions for Java ArrayList
I have been involved in many a java interviews and following are five tricky ones where I found several junior to mid-level Java developers faltering once in a while. Thus, I thought to put an article around these questions to help junior Java developers make familiar with these questions. The article presents the 5 tricky interview questions in relation with Java ArrayList, I believe, could get the interviewee score some browny points, if answered well. Let me know if you agree and would like to add another set of questions to the list below: How does the size of Arraylist increases automatically? Could you share the code? This is the most …
The 7 Habits of Highly Effective Developers

Well, I researched on the internet looking for one or more articles which was written with the title, 7 Habits of Highly Effective People, and found a couple of them that has been written in the recent past. Following are some of them: http://blogs.msdn.com/b/johnwpowell/archive/2008/05/22/the-7-habits-of-highly-effective-developers.aspx http://drupal.technicat.com/writing/programming.html http://css.dzone.com/articles/7-habits-highly-effective The above articles are good and do talk about different aspects of becoming effective developer. However, I was not satisfied much as I could not find mention on some of the points that I wanted to talk about. Following is representation of my views on 7 Habits of Highly Effective Developer. Please feel free to share your opinion on whether I was able to …
How to Increase Unit Test Coverage of Legacy Code?
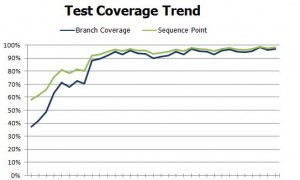
The article represents a time-tested approach on how to increase unit test coverage with legacy code. I shall try and answer following relevant questions in order to present the approach on increasing the test coverage of legacy applications (code). What are some of the key challenges? Leadership Buy-in: As soon as you start planning for writing unit tests on legacy applications, you come to realize that it won’t be very effective and smooth without the consideration of code refactoring. The reason being the fact that legacy code in many cases are found to have very high code complexity in terms of cyclomatic complexity and, familiar code smells such long classes, …
2014 Development Trend: Decouple User Experience from Functionality

The article represents an interesting trend in relation with need for decoupling user experience from functionality that is happening as result of different UI channels such as web, mobile devices using which users could access the software functionality. This can be termed as “Paradigm Shift” that needs to be adopted by developers sooner than later as part of the development practice. This is becoming much more relevant for this year, 2014 where there will be a need for delivering functionality on different devices/channels. What this means is that developers need to stop visualizing user interfaces (UIs) when they analyze the feature/functionality development. This is primarily because of the following reasons: …
4 Reasons Why You Would Want to Create Custom Exceptions?
Either you are writing a program in Java or .NET, the questions remains that why to create custom exceptions in the first place? I, in my initial years as IT professional, also kept wondering on why, at all, there is a need for custom exceptions whenever I use to come across one of these types. At the same time, I also wondered on how to come up with right names for custom exceptions if at all I want to create one. Please feel free to add to the below reasons if you believe that there are other points that should also be covered as part of benefits for creating custom …
6 Java Exceptions that Haunts a Newbie Java Developer
Every now and then, I come across various newbies Java developers who are found to get stuck with some of the following common exceptions where I need to explain them all over again. I do believe that this is same with many other senior Java developers who try and help these rookie developers to deal with following exceptions. Thus, I thought of coming up with this article and use it for myself going forward. Please feel free to comment or add to the below exceptions list. NoClassDefFoundError: This is one of those exception, with message such as Exception in thread “main” NoClassDefFoundError, that has been most commonly found to welcome newbie Java developers to …
3 Java 7 Features Aimed to Enhance Code Quality
There are several new features that have been released in Java 7 to take care of several developers’ requirements. However, interestingly, I have figured out that three of those 7 features are primarily aimed to enhance following key characteristics of code quality. Please feel free to share your opinion on them. Code Readability Code Duplication Code Complexity Following is the detail of those 3 Java 7 features: Underscore in Numeric Literals (Enhances Code Readability) This feature primarily takes care of code readability, and hence, code usability, having large numbers having several digits. For example, credit card number, social security number etc. Many a times, we come across large number which seem to have an embedded …
Top 4 Security Books Developers Would Want to Keep Handy
Off-late I have been doing an extensive research on application security to to come up with application security guidelines (minimum & most important ones) which could prove very handy and at the same time, very useful for different class of IT professionals including developers, and architects. This is where I have come across some of the following books which has helped me to fulfill my objectives. In one of my later blogs, I shall also list down those basic minimum knowledge that is needed by developers to write secure code. In the meantime, allow me to list down top 4 application security books that, I believe, every developer would want …
Tips for Developers to Increase their IQ (Innovation Quotient)?

One of the primary concerns of many software services companies is to figure out how could they increase business with their existing customers year-on-year (YOY). And, one of the sure shot methods to achieve that objective is to provide innovative solutions which directly impacts their customers’ business in a positive manner and leads to increase in their business. This could, in turn, lead to enhancement of engagement & relationship between customer and the software service provider, thus, leading to growth of software service providers’ business. As mentioned above, the definitive way for software service provider to grow their business is to come up with innovative solutions which impacts the customers’ …
Top 5 Code Smells Newbies Developers Could Easily Identify & Avoid

Following is one very popular image which has been used to represent time and again for representing code smells. I am doing it again. Apologies if this one is repeat for some of you. But the image nicely represents how to find if your code really smells. The code smells listed in this article would certainly lead to increase in WTF count 😉 For newbie developers, it has always remained a challenge to write code of great quality from day one. One of the primary concerns they have been found to have is following: What kind of code could be termed as high quality code? There are several characteristics of good …
Top 6 Refactoring Patterns to Help You Score 80% in Code Quality
This blog lists down top code smells and code refactoring patterns which would help you write good quality code. Top 5 Code Smells Have done several code reviews in past and found following top 5 code smells common across most of these code having code quality issues: Large Class: The classes were found larger enough due to lack of developers’ understanding on one of the primary coding principles which is “Single Responsibility Principle” (SRP). These classes use to get larger due to various methods serving unrelated functionality in the same class. Long Method: The methods have been found longer due to several reasons such as following: Several block of code …
List of Handy Architecture & Design Patterns for Developers & Architects
[adsenseyu2] If you are a newbie developer. experienced developer, aspiring to be architect or an architect, you may want to keep following architecture & design patterns handy with you to solve day-to-day software architecture and design problems at your work place. These patterns can be applied for developers/architects of varied experience level, having expertise with various different technologies (programming languages). Please feel free to suggest additional patterns as if I may have missed some of them. Application Architecture Patterns: These patterns primarily are related with topics such as how to layer an enterprise application, how to organize domain logic, how to tie that logic to a relational database, how to design a …
Top 5 Java Forums Worth Frequent Visits for Newbie Java Developers

If you are a newbie Java developer, and want to get your queries clarified quickly along with learning Java in a fast-paced manner, you may plan to visit to some of the following forums on the regular/frequent basis. These forums have been reviewed and listed below on the basis of number of discussion threads and participation/replies from the forum members. These forums could also be frequented by experienced Java developers owing to the fact that various interesting topics related to advanced level Java are also discussed in these forums. [adsenseyu2] CodeRanch.com (http://www.coderanch.com/forums): A very active forum, for Java developers of all expertise level, I personally found this best of the …
How to Estimate A Story in An Agile SCRUM Sprint

Wondering on how to estimate a set of business requirements into one or more Agile SCRUM Sprints? Go on reading further and let me know what you think. If you are planning to work/develop software based on Agile SCRUM development model and are looking out for an estimation model, here it goes. Quick Overview on Agile SCRUM Before I go into presenting the model, let me present a quick introduction to Agile SCRUM development model. Agile software development is a set of software development methods that are based on iterative and incremental method, where requirements and solutions evolve through collaboration between self-organizing, cross-functional teams. Following is taken from Agile Manifesto …
Business Process or Workflow – Chicken or Egg – Who Comes First?
Many a times, you ask the definition of business process or workflow, it so happens that the mention of other happens while a person is trying to define any of them. And, the next moment the question is asked that what is the difference between business process or workflow, and that which contains which one. This article tries to define each one and relate them appropriately while mentioning distinct difference between them? At times, it tends to appear like a chicken or egg situation which represents the fact that whether workflow in your systems may be progressed to define and create business processes (bottoms-up) or business process, once defined, needs to …
Tools to Obfuscate Your Java Classes
If you have got the requirement to demonstrate your tool built using Java on client machine (third party computers) by deploying your entire tool, and you are worried if your critical application jar files consisting of Java classes could get decompiled and seen by others, you could use some of the following tools: Proguard could be used to obfuscate the class files. ProGuard is a free Java class file shrinker, optimizer, obfuscator, and preverifier. In the process of obfuscation, it renames the remaining classes, fields, and methods using short meaningless names. JBCO (Java ByteCode Obfuscator) could transform code to be more complex, esoteric, or otherwise obscure in order to hinder reverse-engineering nad decompilation …
I found it very helpful. However the differences are not too understandable for me