Author Archives: Ajitesh Kumar
Java – How to Create a Binary Search Tree
This article represents the high level concept and code samples which could be used to create a binary search tree in Java. Please feel free to comment/suggest if I missed to mention one or more important points. Also, sorry for the typos. Following are the key points described later in this article: What is a binary search tree? What are different kind of traversals? Code Samples What is a binary search tree? A binary search tree is a binary tree in which every node contains a key that satisfies following criteria: The key in left child is less than the key in the parent node The key in the right …
Java – One-Liner Lambda Expression to Print Map/List Objects
This article represents code samples to print element of collections such as Map and List/Set using lambda expression. I just love it as it has made life so simpler by helping me achieve this using just one line of code. Please feel free to comment/suggest if I missed to mention one or more important points. Also, sorry for the typos. Following are the key points described later in this article: Print Map key-Value Pair using Lambda Expression Print List value using Lambda Expression Print Map key-Value Pair using Lambda Expression Pay attention to forEach function that takes a reference to BiConsumer function interface and prints the key and value. This …
Data Science – Top 5 Videos to Get Started with Neural Networks
This article represents some good youtube videos that I found useful to get started with understanding how brain works and what is neural networks. Note that I needed to do this as I wanted to get started with machine learning and neural network algorithm. In order to do that effectively, I needed to understand what are neural networks and videos below helped me get started within an hour. Please feel free to suggest other great videos which I may have missed. Sorry for the typos. From Neurons to Networks I would rate it as the one of the best videos I saw on how human brain works. MUST watch!!! …
Java – Map & BiConsumer Function Lambda Expression Example
This article represents code samples representing lambda expression and the related ease with which one could print key and value of a Map object using one liner. Please feel free to comment/suggest if I missed to mention one or more important points. Also, sorry for the typos. Code Sample – Printing Map using BiConsumer Functional Interface Following is detail for Map.forEach API in Java 8. Read further on this page. default void forEach(BiConsumer<? super K,? super V> action) Performs the given action for each entry in this map until all entries have been processed or the action throws an exception. Unless otherwise specified by the implementing class, actions are performed in …
Java – How to Scrape Content from a URL

This article represents take-away code sample that could be used to get or scrape content from a given URL. Those wanting to do a quick web scrape could use this piece of code. I shall be posting a series of blogs which would help one to create a web scraper using Java. The reason why I am hooked to Java web scraping is the need to get the data from web for data analysis. Please feel free to comment/suggest if I missed to mention one or more important points. Also, sorry for the typos. Code Sample – Get Content from URL Pay attention to some of the following aspects of fetching …
Data Science – 3 Key Aspects of Applying KMeans Algorithm for Clustering Tasks
This article represents key concepts around KMeans algorithm including key aspects and formula/R command when you are working on clustering tasks. Please feel free to comment/suggest if I missed to mention one or more important points. Also, sorry for the typos. Following are the key points described later in this article: Key aspects of applying KMeans algorithm KMeans Algorithm – R Command Key aspects of applying KMeans Algorithm Key aspects of applying KMeans algorithm are following: Selecting a right combination of features set: On the data set on which you may observe some of the following: There are one or more features having non-numeric or character data sets. As …
Data Science – R Packages & Methods for naive Bayes Classification

This article represents different R packages and related methods which could be used to create a naive Bayes classifier. Please feel free to comment/suggest if I missed to mention one or more important points. Also, sorry for the typos. Following are the key packages described later in this article: TM WordCloud e1071 Gmodels Following is a list of R packages that could be used for naive Bayes classification: TM Package: Originally created by Ingo Feinerer as a dissertation project at the Vienna University of Economics and Business, tm package is a very popular package that provides a framework for text mining applications within R. More about TM package could be …
Learn R – How to Fix Read.Table Command Reading Lesser Rows
This article represents the problem statement related with read.table reading fewer or incorrect or lesser number of lines or rows when reading a text file having multiple columns, and the solution to the same. This is going to be a shorter blog. But since it solved a problem on which I spent some time, I chose to write about the same. Please feel free to comment/suggest if I missed to mention one or more important points. Also, sorry for the typos. Problem Statement: Reading Fewer Lines with read.table Command I have been learning the naive bayes classification. I downloaded this SMS collection data. I went ahead and tried to load …
Data Science – Data Cleaning R Commands for Text Classification Problems
This article represents concepts and related R command set used to clean the text in order to make it ready for text classification. The R command set belongs to tm package. Please feel free to comment/suggest if I missed to mention one or more important points. Also, sorry for the typos. Lets load a set of messages along with appropriate classification using following command. messages <- read.table( file.choose(), sep=”\t”, stringsAsFactors=FALSE) The messages data frame could have two features, such as type and text where each piece of text is associated with an appropriate type. Once done, lets go ahead and create a Corpus object out of all the message text. …
Data Science – Common Exploratory R Commands for Classification Problems
This article represents common exploratory R commands that could used during the stage of data preparation when solving classification problems. I found them being used when I have been going through KNN or naive Bayes algorithms. I know that there may be more to the list below. I would love to hear those additional commands from you. Please feel free to comment/suggest if I missed to mention one or more important points. Also, sorry for the typos. In the set of commands listed below, a data frame, message_text, is used which is a set of text data, loaded using read.table command such as following: messages_text <- read.table( file.choose(), sep=”\t”, …
Productivity – Sublime, AngularJS, Bootstrap Form Template
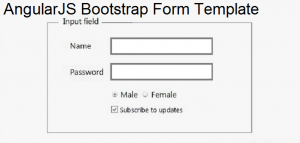
This article represents sublime text editor snippet code sample for an AngularJS-Bootstrap form template which could be used to quickly create an angular app with a simplistic bootstrap form. Please feel free to comment/suggest if I missed to mention one or more important points. Also, sorry for the typos. Following are the key points described later in this article: Why AngularJS-Bootstrap Form Template? How to Create Sublime Snippet? Code Samples – AngularJS-Bootstrap Form Template Why AngularJS-Bootstrap Form Template? Many a times, I wanted to experiment with AngularJS features on an HTML form. This required me to re-write or copy & paste angularjs code and bootstrap form code and create …
Data Science – List of Key Machine Learning Algorithms
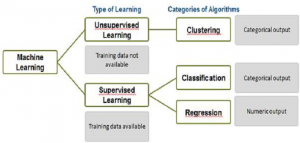
This article represents a list of key machine learning algorithms which are most widely used by data scientists while doing data analysis. Please feel free to comment/suggest if I missed to mention one or more important points. Also, sorry for the typos. The list of machine learning algorithms presented below covers some of the most important and widely used algorithms which could set a stage for one to get started with data science/analytics and create models for predictions. Following are two high level classifications in which these machine learning algorithms fall under: Supervised learning Unsupervised learning Following are some of the key tasks that are performed by machine learning algorithms …
Learn R – How to Add New Column to Data Frame
This article represents concepts and code samples on how to add new columns to a data frame using R programming language. Please feel free to comment/suggest if I missed to mention one or more important points. Also, sorry for the typos. Lets create a student data frame. Following is the code: # Create non-empty data frame with column names # Assign names to x x <- c( “Calvin”, “Chris”, “Raj”) # Assign names to y y <- c( 10, 25, 19) # Create a non-empty data frame with column names # Assign x to “First Name” as column name # Assign y to “Age” as column name student <- data.frame( …
AngularJS – Sublime Template for Hello World
This article represents sublime snippet code sample which you could use to create an auto-complete hello world template to quickly get started with Hello World code for AngularJS. Please feel free to comment/suggest if I missed to mention one or more important points. Also, sorry for the typos. Following are the key points described later in this article: Why Sublime Snippet for AngularJS Hello World How to Create HelloNG Snippet? Code Samples Why Sublime Snippet for AngularJS Hello World Many a time, while starting on new AngularJS app for doing quick POC or testing purpose, I ended up creating boilerplate code or copied and pasted minimum AngularJS app code …
Learn R – How to Convert Columns from Character to Factor
This article represents different ways in which one or more columns in a data frame could be converted to factor when working with R programming language. Please feel free to comment/suggest if I missed mentioning one or more important points. Also, sorry for the typos. Following are the key points described later in this article: Convert single column to factor Convert multiple columns to factor Following data frame, df, is used in the code sample below: In above data frame, both diagnosis and param_d are character vectors. One could quickly check classes of all columns using the following command: Convert Single Column to Factor Following is demonstrated the code samples …
Data Science – How to Scale or Normalize Numeric Data using R
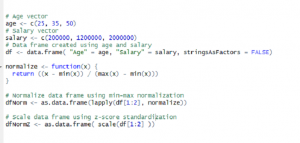
This article represents concepts around the need to normalize or scale the numeric data and code samples in R programming language which could be used to normalize or scale the data. Please feel free to comment/suggest if I missed mentioning one or more important points. Also, sorry for the typos. Following are the two different ways which could be used to normalize the data, and thus, described later in this article: Why Normalize or Scale the data? Min-Max Normalization Z-Score Standardization Why Normalize or Scale the data? There can be instances found in data frame where values for one feature could range between 1-100 and values for other feature could …
I found it very helpful. However the differences are not too understandable for me