[adsenseyu2]
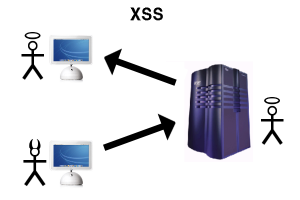
Before we go and discuss the PHP coding tips and techniques to avoid Cross-site scripting (XSS) attacks, lets try and understand quickly what is XSS attack.
XSS is a Web-based attack performed on vulnerable Web applications which ends up victimizing the end user rather than the application itself. In these attacks, malicious content is delivered to users primarily using JavaScript. The XSS attack happens when the web applications accepts the input from the end user without validating it. In XSS attack, the malicious code executes in the context of the victim’s session, allowing the attacker to bypass normal security restrictions. There are multiple good web pages to read about XSS such as OWASP, Wikipedia etc.
- Setting up OWASP ESAPI Library: Following are instructions to download and setup OWASP ESAPI Library for PHP
- Download Tortoise SVN (32 bit or 64 bit) based upon your development environment (system) configuration. Once downloaded, install the SVN. To ensure that it is installed properly, right click anywhere on your system and you shall be able to see the link “SVN Checkout”.
- Right click on desktop and click “svn checkout”. Paste the following link and download. Download PHP library for OWASP ESAPI. This files could be checked out from http://owasp-esapi-php.
googlecode.com/svn/trunk/. - The files get downloaded inside the folder owasp-esapi-php.
- Configuring custom OWASP adapter: Following are instructions to download and configure custom OWASP adapter to work with OWASP ESAPI download above.
- Create a “security” folder in your project and put the entire folder, owasp-esapi-php within this folder.
- Download additional files (put inside security folder in the zip; copy these files) and put inside the security folder where you have put owasp-esapi-php folder mentioned above. One file is a security adapter, OWASPAdapter, which instantiate ESAPI object and assigns appropriate encode and validator. Other is SecurityFilter which works with OWASPAdapter to validate the input parameters. All other classes such as controllers instantiates the SecurityFilter and filters the input parameters against the XSS related inputs.
- Using the code in Controllers to sanitize requests against XSS
- As said in above point, instantiate SecurityFilter in your controller files and filter the inputs against XSS inputs using following code. You may try and test with inputs from XSS cheatsheets (http://sage.math.washington.
edu/home/wstein/www/home/agc/ lit/javascript/xss.html) define( 'ROOT', $_SERVER['DOCUMENT_ROOT'] ); include_once( ROOT . '/security/SecurityFilter.php' ); $secFilter = new SecurityFilter(); $request = $secFilter->sanitize( $_POST ); // In case, you are using $_GET, use $_GET instead.
The above code should be put as one of the first code in your controller to sanitize input requests, before further processing. The $request array will have all the javascript code removed, thus, avoiding XSS attacks that is done primarily using Javascript code.
- As said in above point, instantiate SecurityFilter in your controller files and filter the inputs against XSS inputs using following code. You may try and test with inputs from XSS cheatsheets (http://sage.math.washington.
Above steps would help you get setup with security coding to avoid XSS within no time.
- Questions to Ask When Thinking Like a Product Leader - July 3, 2025
- Three Approaches to Creating AI Agents: Code Examples - June 27, 2025
- What is Embodied AI? Explained with Examples - May 11, 2025
For the file “OWASPAdapter.php”, I found following code:-
“require_once( ROOT . “/security/owasp-esapi-php/src/reference/WebValidator.php”);”
But WebValidator.php doesn’t exist in “owasp-esapi-php”. Please help! Thank you very much!
seems that WebValidator is a customization of
owasp-esapi-php/src/reference/DefaultValidator.php
unfortunately it doesn’t come with default code… i would be interested in it too!
Did you find the WebValidator.php , i have the same problem, webValidator.php not exist!!