
[adsenseyu2]
One of the OWASP top 10 application security vulnerability is Security Misconfiguration. One of the most common way to identify the security misconfiguration configuration is to check if error handling reveals stack traces or other informative error messages to users.
I tried and run an automated scanner on this website, http://www.davrohini.org/ and got various different URLs which revealed stack traces including some of the following:
- http://www.davrohini.org/user/users.jsp
- http://www.davrohini.org/user/snews.jsp
- http://www.davrohini.org/user/left.jsp
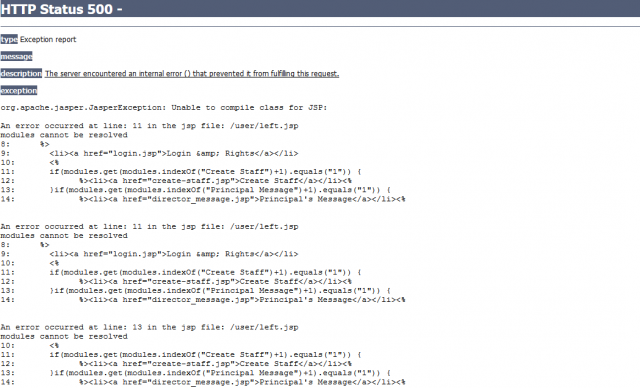
However, the most dangerous one of the above is http://www.davrohini.org/user/left.jsp. Take a look at the screenshot below.
- Security Misconfiguration Example – Showing compilation errors
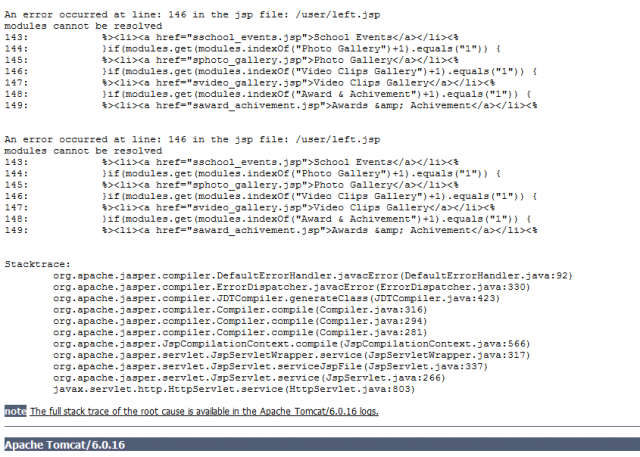
Take a look at another diagram below that shows the information regarding the server Apache Tomcat 6.0.16.
Following is some of the information that can be retrieved by a hacker:
- The application is written in Java/JSP
- The application runs on Tomcat 6.0.16
Following may be one of the approach used for hacking the website:
- One may find the security vulnerabilities associated with tomcat 6.0.16. This can be done by quick google search with following keyword phrase: “Apache Tomcat 6.0.16 vulnerabilities“. You could find specific tomcat vulnerabilities on this page.
- Session hi-jacking
- Elevated privileges: This belongs to E (Elevation of Privilege) of STRIDE model. In this type of threat, an unprivileged user gains privileged access and thereby has sufficient access to compromise or destroy the entire system.
- Information disclosure: This belongs to I (Information Disclosure) of STRIDE model. Information disclosure threats involve the exposure of information to individuals who are not supposed to have access to it—for example, the ability of users to read a file that they were not granted access to, or the ability of an intruder to read data in transit between two computers.
- Data integrity: This belongs to T (Data tampering) of STRIDE model. Data tampering involves the malicious modification of data.
- Mathematics Topics for Machine Learning Beginners - July 6, 2025
- Questions to Ask When Thinking Like a Product Leader - July 3, 2025
- Three Approaches to Creating AI Agents: Code Examples - June 27, 2025
I found it very helpful. However the differences are not too understandable for me