Following are the key points described later in this article:
- What is SAML?
- How does SSO authentication happen using SAML?
- What are Key Components of SSO Design, in general?
What is SAML?
For those of you unaware of what is SAML, here is the definition from WIKIPedia page on SAML:
Security Assertion Markup Language (SAML, pronounced sam-el[1]) is an XML-based, open-standard data format for exchanging authentication and authorization data between parties, in particular, between an identity provider and a service provider. SAML is a product of the OASIS Security Services Technical Committee. SAML dates from 2001; the most recent major update of SAML was published in 2005, but protocol enhancements have steadily been added through additional, optional standards.
The single most important requirement that SAML addresses is web browser single sign-on (SSO). Single sign-on is common at the intranet level (using cookies, for example) but extending it beyond the intranet has been problematic and has led to the proliferation of non-interoperable proprietary technologies. (Another more recent approach to addressing the browser SSO problem is the OpenID protocol.)
Simply speaking, SAML is a XML-based data exchange format used for federated authentication and can be used in Single Sign-on (SSO) implementation.
Following diagram represents SAML-based authentication. In the diagram below, salesforce app acts as a service provider and the identity provider resides in the organization specific data center. When the organizations’ users request one or more protected resource from partners website such as salesforce.com website, the salesforce.com app directs the users request to the identity provider which then processes the SAML request and sends back the SAML response appropriately, thereby authenticating the user.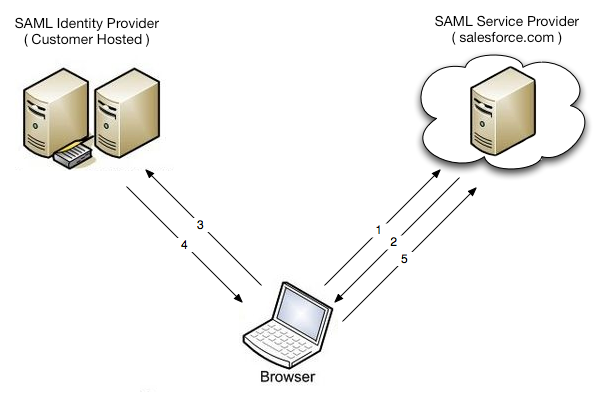
How does SSO authentication happen using SAML?
Following are two key components (actors) of SSO-based authentication:
- Identity Provider: Identity provider hosts the user credentials and is used to authenticate the users. The identity provider could be internal or external providers.
- Service Provider: Service providers are the ones who would like users to be authenticated by identity provider before giving access to its information/resources to the users.
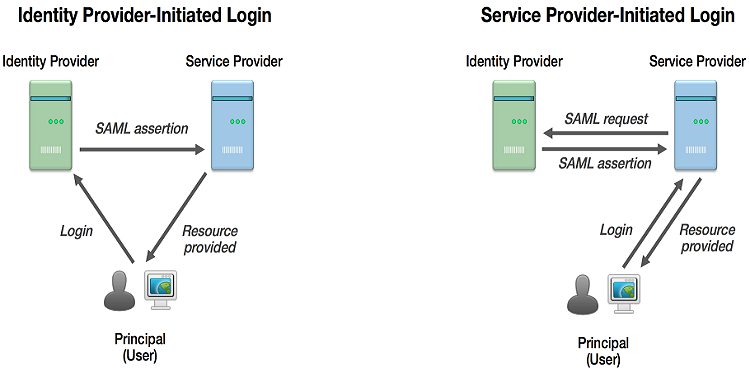
Following are two approaches to SAML-based federated authentication implementation:
- Service provider initiated SAML: In service-provider initiatied usecase, the user attempts to access a resource on the service provider. However, they do not have a current login session and their federated identity is managed by the identity provider. The users requests are sent to the identity provider server for authentication. The identity provider appropriately provides a SAML web SSO assertion for the users’ federated identity back to the service provider. Read further details on this page
- Identity provider initiated SAML: In identity-provider initiatied usecase, instead of visiting the service provider directly, the user accesses the Identity provider site and clicks on one of the links to gain access to the remote servie provider. This triggers the creation of a SAML assertion which is, then, transported to the service provider. The identity provider is configured with specialized links that refer to the desired service providers. Read further details on this page
Following diagram represents both identity and service provider and related flows based on who (service provider or identity provider) initiates the SAML authentication.
Following is how the flow happens for federated authentication using SAML data-exchange format/standard when users requests are initiated by the service providers:
- Users try to access the protected resource on one of the applications (service providers).
- Applications (service providers) create a SAML request and redirects browser to SSO URL (representing identity provider).
- The redirected requests land on to identity provider server.
- Identity provider parses the SAML request, authenticates the users.
- Identity provider generates SAML response, encodes it and send it to the browser.
- The browser sends the response to the service provider.
- The service provider verifies the response and appropriately gives access to protected resource.
What are Key Components of SSO Design, in general?
Following are key points:
- Authentication/Authorization protocol
- Identity provider which provides SSO-based authentication
- Directory Server which may used by identity provider for looking up users credentials
- Service providers that are applications looking to adopt SSO
- Data exchange format such as SAML
- Three Approaches to Creating AI Agents: Code Examples - June 27, 2025
- What is Embodied AI? Explained with Examples - May 11, 2025
- Retrieval Augmented Generation (RAG) & LLM: Examples - February 15, 2025
Hi Ajitesh,
I am currently working in MNC on a Java application which needs to be configured for SSO service. I learnt that i need to implement SAML into my Java application. I walked through a lot of Google information on SAML however i am unable to implement it completely. At present i am working on the instructions provided on below link.
http://docs.spring.io/spring-security-saml/docs/1.0.0.RELEASE/reference/html/chapter-quick-start.html
Do you have a sample Java application which implements SSO? If yes then could you please provide me step by step implementation of the same into Eclipse(using Java 6 & Tomcat 7).
Thanks,
Kishor Singh