
Why two factor authentication?
With the increase in password theft, phishing attacks and other hacking techniques, the conventional text based user name and password based authentication seem to be insufficient because of the rapid rise of network level threats. The traditional way of just memorizing the password to validate one’s identity is not enough and web sites and applications are now expecting one to possess email Id or a smartphone to communicate with another short-lived randomized password, One Time Password (OTP), as one more factor to the authentication. Here we will discuss the approach to generate the OTP and use it for the two factor authentication technique. In the next article, we’ll discuss the implementation of the OTP using the Spring Security framework.
Token Generation using TOTP algorithm (RFC 6238)
One Time Password, as the name suggests, can be used only once and are generally time bound. While this poses some challenge to the hackers, but, the algorithm and authentication protocol to generate and authenticate the OTP will define the real challenge. There can be various ways to generate the OTP but we’ll discuss here the standard based approach using HMAC based One-Time Password (HOTP) algorithm based on RFC 4226 to support event based moving factor. A time-based variant of the same algorithm provides short-lived OTP values based on RFC 6238 (TOTP), which are desirable for enhanced security of the application using two factor authentications. The steps to generate the OTP as per the specification are:
- Generate a random secret key K
- Get the counter i.e. Time of Epoch/30 as the message
- Create Hash of the message using the key K and hash method HMAC-SHA1 or SHA-1
- Get the least significant 4 bits of the hash as offset O
- Get the truncated hash of 4 Bytes starting from the offset value
- Remove the first bit of truncated hash to take the unsigned value (32 bit Integer) I
- Token is lowest N digits of I on base 10.
- If the Token has less than N digits, pad the token with 0 from the left to make it N digits.
One can implement the RFC 6238 specification by following the above steps and generate the OTP to be used for the two-factor authentication. The alternate way could be to use the implementation provided by Google as service and generate the OTP as Google Authenticator, a six digit token.
Implementation of two-factor authentication
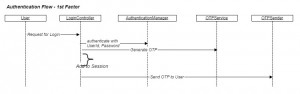
The first approach in the implementation of the two factor authentication mechanism is to authenticate the first factor using the conventional Username and Password based authentication. There needs to be an authentication manager which will authenticate against the User data store such as LDAP, database or any other service storing the user credentials. The OTP service will generate an OTP using the algorithm as per TOTP algorithm defined above which can be stored in user session or the persistent store. The generated authentication token can be sent using the OTP sender service on the smartphone or the email. The sequence diagram below depicts the entire flow of the first factor authentication and OTP generation.
The flow in the above sequence diagram is:
- LoginController handled the user requests and passes the credentials to the AuthenitcationManager for authentication.
- On successful authentication of the user credentials, the session is established and the request to OTPService is sent to generate the OTP token.
- The OTP token is stored in the user session or persisted in the database.
- LoginController then sends the OTP token to the user using the registered mobile number or the email ID.
- User is displayed the next page to provide the OTP authentication token and complete the authentication.
- Till the time, User can be assigned a role of pre OTP authenticated user (e.g. PRE_OTP_AUTHENITCATED_USER) to allow limited access of the protected resources.
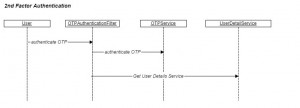
The second step in the entire flow is to validate the OTP token provided by user. The OTP authentication filter authenticates the token and if the token is valid and matches against the one stored in the user session or the persistent store, it provides the access to the protected resources. The steps to complete the 2nd factor authentication flow are:
- User provides the OTP token and submits the token to the server.
- The OTPAuthenticationFilter validates the token and authenticates against the one stored in the user session by calling the OTPService.
- UserDetailsService loads the details of the user in the session and the user Principal is created in security context.
- User is assigned the role of authenticated user (e.g. AUTHENITCATED_USER) to access the protected domain resources.
Two Factor flow can be implemented using any standard security framework. We’ll provide the Spring Security and JEE related implementation in the next article.
- Authentication using One Time Password (OTP) technique – Part 1 - September 22, 2014
Have you posted the second part to this post (Spring configuration for one time password implementation)? I am looking to implement this shortly and have been hunting around for a good guide. I am actually doing this via Grails, but using Spring Security under the covers.
Thank you!
Great Article – Any update on this? Looking forward to see Part 2.
Can you please share the link for part 2.
great article. upload part2 Spring Security and JEE related implementation .
thank you
Please give me a simple answer to a simple question:
tell me where am I supposed to put the otp I am given when I am trying to sign in to my account?
w